
Ubuntu - Spectre - Meltodwn | A kind tuto to help
- 6 minsStart new writing about “Why & How to protect your labtop”
The purpose is :
- Prepare it in english language in order to facilitate collaboration
- Write & publish and then translate in French language in order to help french people
- Use github as a back office.
Table of contents
- What is Spectre & Meltdown
- 1.1 why it’s important for every people
- 1.2 But at the End…
- Check
- 2.1 Your Processor
- 2.2 Your distribution & some system informations
- 2.3 Migration or Upgrade your OS
- Use a smple command line
- Use spectre-meltdown-checker
- 4.1 Install
- 4.2 Run the script
- What are your choices ?
- 5.1 Lottery ?
- 5.2 Check your CPU activity
- 5.3 Patch ?
- Pacth it ! ? Huhuh
- 6.1 Patching Spectre and Meltdown Vulnerabilities
- 6.2 Check
- 6.3 Upgrade & Reboot & Check
- 6.4 And Now ?

1. What is Spectre & Meltdown
“The issue potentially affects millions of laptops globally.” : see paper
In 2007, OpenBSD mailing list knew about flaw risks, see : disussion
Dedicated to Ubuntu’s wiki
1.1 why it’s important for every people
“Meltdown and Spectre: ‘worst ever’ CPU bugs affect virtually all computers”
Everything from smartphones and PCs to cloud computing affected by major security flaw found in Intel and other processors – and fix could slow devices, source the Guardian
1.2 But at the End…
- On va tous mourir
- Démontez vos processeurs Intel tout de suite
#CyberApocalypse
#CyberArmagédon
#CyberFinDuMonde
2. Check
2.1 Your Processor
$ cat /proc/version
e.g
Linux version 4.13.0-32-generic (buildd@lgw01-amd64-016) (gcc version 7.2.0 (Ubuntu 7.2.0-8ubuntu3)) #35-Ubuntu SMP [Date]
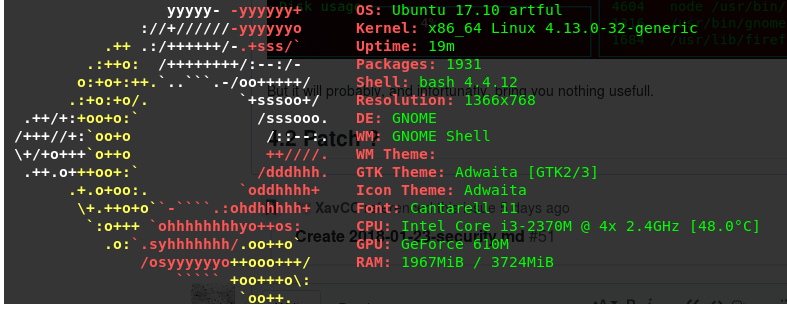
2.2 Your distribution & some system informations
Using screenfecth
$ screenfetch
2.3 Migration or Upgrade your OS
` $ do-release-upgrade –help`
Here are some of the most useful options:
$ do-release-upgrade --check-dist-upgrade-only
The -check-dist-upgrade-only option checks whether a new version exists. If a new version is found, it is displayed as a result in the terminal. Executed in this way, this command only performs a check no upgrade is done.
$ do-release-upgrade --sandbox
The --sandbox option allows you to test an upgrade in a protected environment. This is particularly useful for testing the deployment of an upgrade before it is applied in the production environment.
$ sudo apt-get update
$ do-release-upgrade
upgrade without interaction
$ do-release-upgrade -f DistUpgradeViewNonInteractive
Without options, the do-release-upgrade tool searches and upgrades to the next available LTS or stable version, if available.
3. Use a smple command line
(source)
curl https://raw.githubusercontent.com/speed47/spectre-meltdown-checker/master/spectre-meltdown-checker.sh | bash
Notes
[1] This is a perfect example of what you should avoid to do as a root user without having read and understood the sources, or really trust the author
[2] Mozilla mentionned Spectre & Meltdown mitigation in Firefox starting from version : 57.0.4
4. Use spectre-meltdown-checker
4.1 Install
using wget:
$ wget https://raw.githubusercontent.com/speed47/spectre-meltdown-checker/master/spectre-meltdown-checker.sh
Or if you prefer to use Curl:
$ curl https://raw.githubusercontent.com/speed47/spectre-meltdown-checker/master/spectre-meltdown-checker.sh --output spectre-meltdown-checker.sh
Then
4.2 Run the script
According to the permissions that you have for the file, you may be able to execute it using the following command (if you used chmod +x):
$ sudo spectre-meltdown-checker.sh
Otherwise without adding permissions to the file, just run the script using sudo bash:
$ sudo bash spectre-meltdown-checker.sh
This will start the tool and in matter of seconds you will know if your processor is vulnerable to Spectre or Meltdown:
5. What are your choices ?
5.1 Lottery ?
$ sudo apt-get update
$ sudo apt-get dist-upgrade
Move from Ubuntu 16.04 to Ubuntu 17.10 « The Artful Aardvark » doesn’t change anything to the flaws.
5.2 Check your CPU activity
‘Cause those security flaws affect your cpu’s activity
Using gtop
$ curl -sL https://deb.nodesource.com/setup_8.x | sudo -E bash -
sudo apt-get install -y nodejs
then ` $ sudo npm install gtop -g`
Run ` $ gotp` 
By the way, it seems
s-tuihad some toubles with Ubuntu, so I Open an Issue
it works with sudo su
pip install s-tui
s-tui
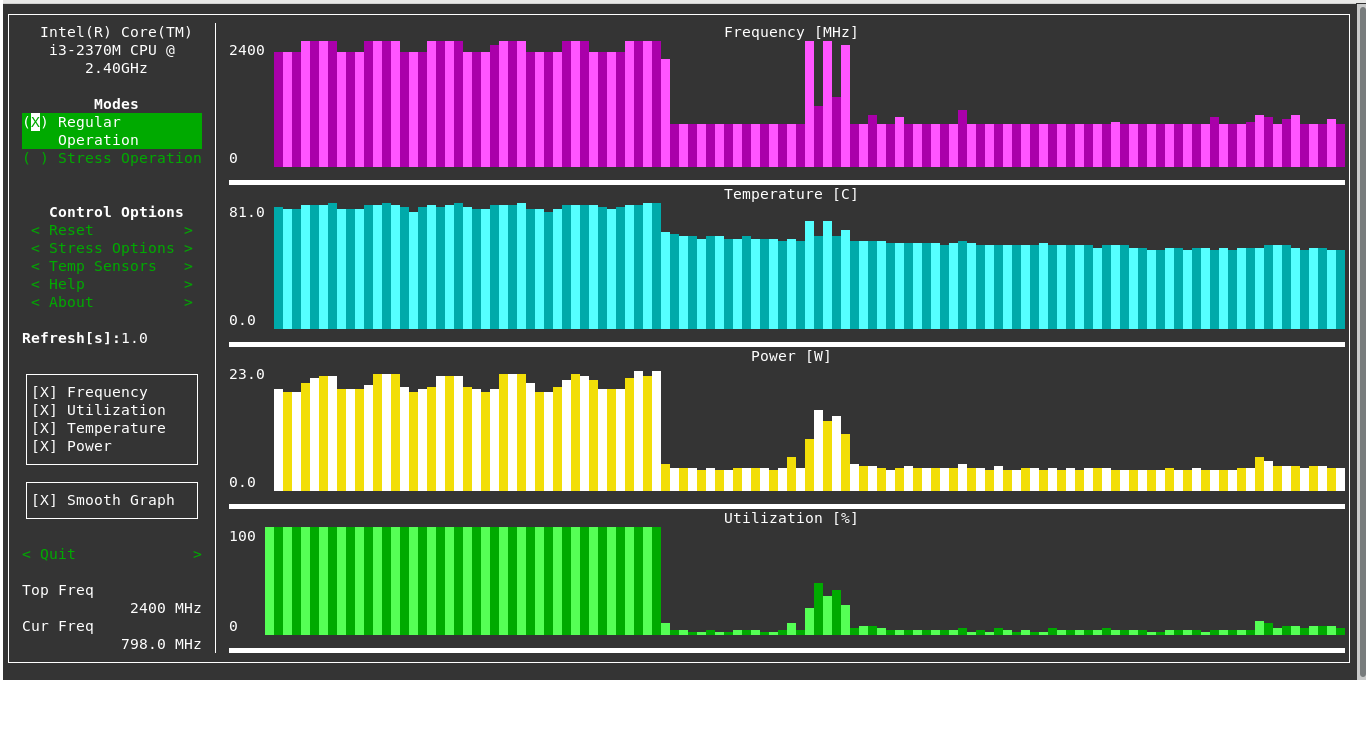
But it will probably, and infortunatly, bring you nothing usefull. Just find indication about activity on your CPU, it’s only monitoring, it’s not about acces and user privilege ont the central processing unit. On the other hand, you may be able to see if your labtop is used to undermine the currency for some other undesirable :-D
5.3 Patch ?
Yes you can !!! finally, partially - or not !
6. Pacth it ! ? Huhuh
6.1 Patching Spectre and Meltdown Vulnerabilities:
Spectre and Meltdown patches are delivered as kernel updates on Ubuntu 17.10. Ubuntu 17.10 has been releasing kernel updates as Spectre and Meltdown vulnerabilities are fixed.
To get these kernel updates, you must have ‘artful-security’ and ‘artful-updates’ repository enabled. To check whether these repositories are enabled, go to the Applications menu and look for “Software & Updates”. You should see “Software & Updates” app as shown in the screenshot below. Click on it
“Software & Updates” should open. Now click on the marked tab “Updates”.
Then You should see the following window. Click on “Reload”. Ubuntu should update its package repository cache.
6.2 Check
Check the version of Kernel you’re using on your Ubuntu 17.10 Artful Aardvark operating system with the following command:
` $ uname -r`
You can see that the version of kernel
e.g 4.13.0-25-generic
6.3 Upgrade & Reboot & Check
Now run the following command to update all the available packages of your Ubuntu 17.10 operating system:
` $ sudo apt-get upgrade` then
` $ reboot`
after your computer restart
` $ uname -r`
If, on your terminal, you have something like “Some packages have been kept back linux-generic linux-headers-generic linux-image-generic ubuntu-desktop”
do
$ sudo apt-get install linux-generic linux-headers-generic linux-image-generic ubuntu-desktop
After all those actions Your kernel should be updated.
$ uname -r
4.13.0-32-generic
Fot Ubuntu 17.10 Artful Aardvark.
6.4 And Now ?
$ sudo bash spectre-meltdown-checker.shand Compare with your 1st try- Be vigilant and keep track of upcoming changes and patches
- Updates Instructions, 2018 Jan 22: Ubuntu kernel updates addressing all three vulnerabilities (CVE-2017-5715, CVE-2017-5753, CVE-2017-5754) across amd64, ppc64el and s390x are released in USN-3541-1 (Ubuntu 17.10), USN-3540-1 (Ubuntu 16.04 LTS), USN-3541-2 (Ubuntu 16.04 LTS (HWE)), USN-3542-1 (Ubuntu 14.04 LTS) and USN-3540-2 (Ubuntu 14.04 LTS (HWE)).
did you learn something ?
Please be human, share it ;-) or contribute
Merci à toutes les personnes qui soutiennent les efforts par leurs dons